UPDATE 8/31 at 2:15pm PT Since our original post, there have been many reports about the exposure of 68 million Dropbox credentials from 2012. The list of email addresses with hashed and salted passwords is real, however we have no indication that Dropbox user accounts have been improperly accessed. We’re very sorry this happened and would like to clear up what’s going on. If you signed up for Dropbox before mid-2012 and reused your password elsewhere, you should change it on those services. We recommend that you create strong, unique passwords, and enable two-step verification. Also, please be alert to spam or phishing because email addresses were included in the list.
If you signed up for Dropbox prior to mid-2012 and haven’t changed your password since, you’ll be prompted to update it the next time you sign in. We’re doing this purely as a preventive measure, and there is no indication that your account has been improperly accessed. We’re sorry for the inconvenience.
What do I need to do?
If prompted, all you need to do is choose a new and strong password. We provide a password strength meter to help you. If you don’t receive a prompt, you don’t need to do anything. However, for any of you who’ve used your Dropbox password on other sites, we recommend you change it on Dropbox and other services. We also recommend that you enable two-step verification.
Why we’re doing this
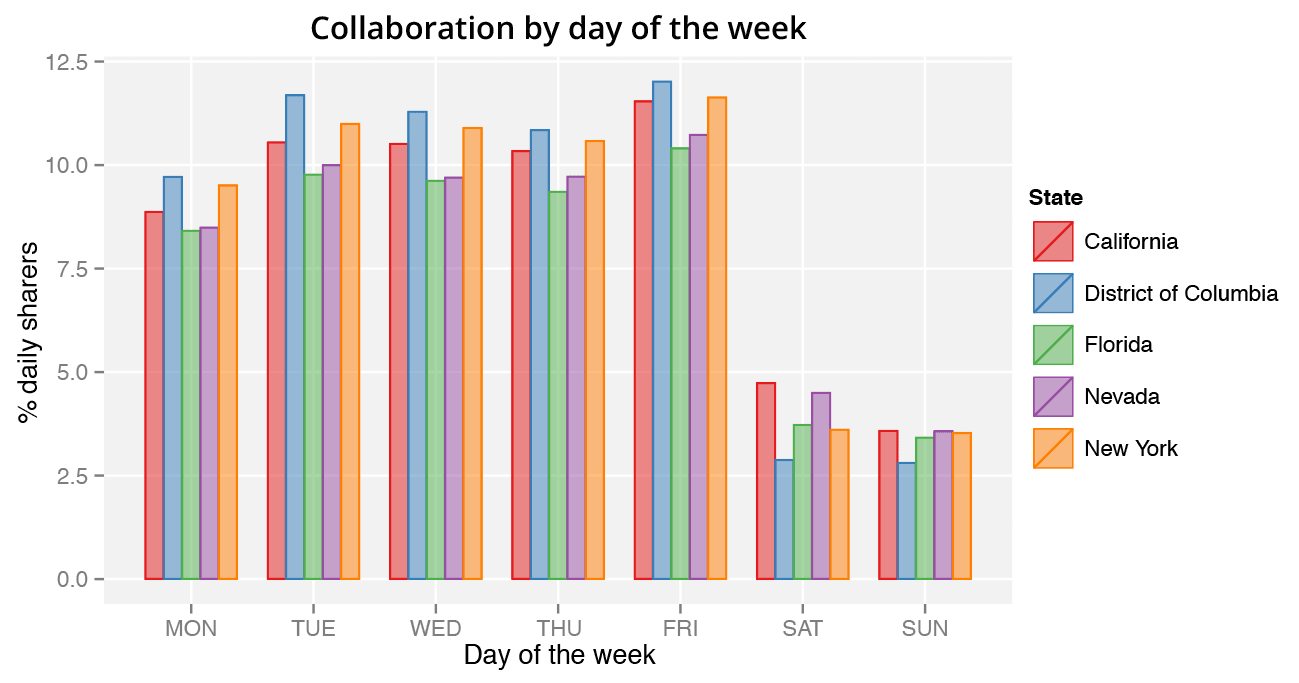
Our security teams are always watching out for new threats to our users. As part of these ongoing efforts, we learned about an old set of Dropbox user credentials (email addresses plus hashed and salted passwords) that we believe was obtained in 2012. Our analysis suggests that the credentials relate to an incident we disclosed around that time. Based on our threat monitoring and the way we secure passwords, we don’t believe that any accounts have been improperly accessed. Still, as one of many precautions, we’re requiring anyone who hasn’t changed their password since mid-2012 to update it the next time they sign in.
Our ongoing security practices
We have dedicated security teams that work to protect our services and monitor for compromises, abuse, and suspicious activity. We’ve implemented a broad set of controls including independent security audits and certifications, threat intelligence, and bug bounties for ethical hackers. In addition, we build open source tools such as zxcvbn, use bcrypt password hashing, and offer Universal 2nd Factor authentication to all users.
For more information
To learn more about keeping your account secure, please visit our security and privacy page. If you have any questions, feel free to contact password-reset-help@dropbox.com. Patrick Heim is Head of Trust & Security for Dropbox.